Article Everything You Need to Know About Microsoft Office 365 Document Security
By Insight Editor / 29 Jan 2019 / Topics: Microsoft 365 , Software

Malicious attacks, internal data transfers, employee access errors, and improper data encryption are only some of the culprits that affect document security, but switching to Microsoft Office 365 ensures that your documents are well protected in the cloud.
The necessity for your business-related documents to remain safe and secure in the cloud is increasingly important as we all start using our Surface Pros and other devices outside of the business environment.
The reliability and portability of these devices have been touted as completely replacing our laptops, but we’ll still always be concerned about the security of our documents.
IBM and Ponemon Institute released their Cost of Data Breach Study: Global Analysis and reported that the average total cost of a breach was $3.79 million.
The year 2014 was viewed as the “year of the breach” and saw a record number of businesses and industries exposed to malicious attacks that put their business operations at risk by exposing their sensitive internal documents.
At a cost of $154 per record breach, it’s no surprise that 75% of security leaders expect their security budget to dramatically increase in the next three to five years to prevent these costly breaches.
Ensuring that your sensitive documents are accurately controlled and monitored is critical to preventing data loss or corruption. This can easily be achieved through the cloud-based Office 365.
Protecting Documents
With the proliferation of BYOD and advanced collaboration technology, enterprise businesses need stricter controls and access limitations on documents.
One serious concern when it comes to sharing documents through email is how easy it is for the recipient to download, print, or distribute it.
With Microsoft Rights Management Services (RMS), you can attach limitations to a document in order to prevent opening, editing, copying, forwarding, or printing.In order for the recipient to open it, they are required to enter a password.
Therefore, anyone not in the communication thread or anyone without a password cannot access the encrypted file.
Also with Microsoft RMS, you can set an expiration date that completely restricts access and, after a specific amount of time, the document will technically self-destruct on the receivers end, obliterating all access allowances in the process.
Document formats such as Word, Excel, and PDF can be stored and shared from OneDrive or SharePoint Online to enable collaboration, but protective measures established on individual or groups of documents will still apply.
Protection travels with the document.
Protecting Identities
The proliferation of mobile devices, from phones to tablets, makes it difficult to manage user identities.
Microsoft Office 365 for business can establish a connection with the Azure Active Directory that communicates with on-site directories for stricter identity management.
According to the IBM study, 43% of C-level executives say the highest threat to sensitive data is due to negligent internal staff.
This is one of the reasons that Office 365 has mandatory background checks built in for high privilege access. This highly scrutinized, manual-approval process ensures that access isn’t accidentally given and that the job functions meets the access levels.
This high privilege access can include anyone that can oversee the business, as well as IT department individuals with access to change identity allowances.
Setting up workforce-wide profiles that limit access and employing multi-factor authentication controls will ensure that sensitive documents remain for the eyes of the employees they were meant for — and no one else.
These multi-factor authentications can be set-up to require a password that was sent to an approved user’s smartphone, ensuring that both a password and the user’s phone is used to access.
An added bonus to multi-factor authentication is an immediate notification when someone is trying to access your account.
This allows your IT team to address the situation as it happens, and not rely on noticing this hack later on down the line, when potentially huge amounts of data could have already been stolen.
The quicker a breach is noticed, the less damage that can be done.
Hackers are rarely looking for one specific file. If they don’t have the leisure at which to peruse and download, the likelihood of them accessing businesses and damaging files is limited.
Furthermore, Active Directory controls force employees to change passwords after 90 days, include the use of CAPTCHA techniques and lockouts after numerous failed attempts.
These additional controls ensure that you’re forcing your employees to use strong and smart passwords that can’t be easily hacked.
Protecting Data
The IBM Cost of Data Breach Study reported that 47% of breaches are due to malicious attacks, but their extensive use of encryption saved an approximate $12 per record breached.
In Microsoft Office 365 for business, all email and data at rest are encrypted using BitLocker 256-bit AES Encryption. This data protection feature is integrated into both the server’s operating system and the computer to address any threat of data theft or exposure.
Since malware anomalies occur more frequently during off-work hours, (2,157 between 8pm-8am, compared with 987 from 8am-8pm) Microsoft Office 365 runs a threat management policy of “assume breach.”
This assumes that something has already happened in your cloud storage and is simply not known so that teams are continuously attempting to detect and mitigate threats.
Through Exchange Online, numerous preventions are made to ensure email protection on incoming mail, as well as outgoing mail that includes sensitive information.
Data loss prevention (DLP) technology identifies, monitors, and protects sensitive data and alerts users to the risk. DLP can monitor email messages and attachments for sensitive information such as credit card numbers and alert users before they send.
Users can simply be warned, answer a request for authorization, or be blocked from sending data completely.
Furthermore, Exchange Online includes advanced anti-spam capabilities to assign a spam confidence level (SCL) value to incoming mail to be deleted, put in spam, or delivered to inbox.
Protecting the Hardware
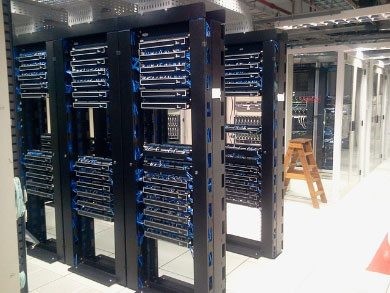
All Office 365 data is stored in a multi-tenant environment in Microsoft’s data centers, which are in undisclosed locations and run by Microsoft Global Foundation Services.
These servers are strategically located in multiple regions throughout the world and all data in transit is encrypted using industry-standard transport layer security (TLS) and secure sockets layer (SSL).
The segmented networks provide complete separation of critical back-end servers and storage devices from the public-facing interfaces, and all servers are well-protected against physical breaches.
Through the requirements of badges, smart cards, biometric scanners, and two-factor authentication, employees in the 24/7/365 centre are granted access only once they’ve proven their identity.
Furthermore, the data centers are monitored using motion sensors, continuous video surveillance, security alarms, and on-premise officers.
In the event of a natural disaster, data centers are outfitted with seismically braced racks and automated fire prevention and extinguishing systems.
According to the IBM study, businesses who employed an incident response team and had thorough disaster recovery and business continuity plans saved $12.60 per breached record.
Conclusion
If you’ve been considering creating a more collaborative environment for your sensitive documents, but are concerned about how to properly protect them, Microsoft Office 365 could be the answer.
Insight is a certified Microsoft partner and can assist in the procurement, deployment, and monitoring of your cloud; whether a public, a private or a hybrid cloud environment.
With over 30 years of experience as a VAR and MSP, we understand your business needs and can consult on the best solutions to help you meet your goals. Give us a call today to inquire about Office 365 and we’ll guide you through the entire process.